Solution Functions

What we do. How we do it.
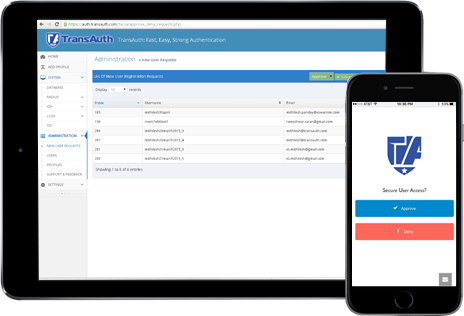
At our core, we are a hybrid solution that combines four key access control technologies into one flexible, elegant package.
Multifactor Authentication
Increase security by decreasing the risk of compromised credentials.
Single Sign On
Reduce identity sprawl and password fatigue by giving users a single identity.
Credential Management
Passwords are still one of the most flexible single factors available.
Password Management
Generate, store and recall strong passwords for any system with the Agent’s integrated password manager.
Password Sharing
Shared accounts pose additional risks due to insecure sharing practices. Keep passwords safe by using integrated password sharing.
Password Self-Service
Reduce helpdesk calls by allowing users to reset and recover locked or forgotten passwords directly from their login screen with TransPASS.
Endpoint Protection
Endpoints represent the broadest surface area of any organization.
Login Security
Secure access to laptops, desktops and servers with the manual or automatic multifactor authentication.
Proximity Awareness
Prevent unattended workstations from posing a threat to sensitive resources by enabling proximity locking.
Data Encryption
Use TransCrypt to protect sensitive data by automatically encrypting files when the user is not present.