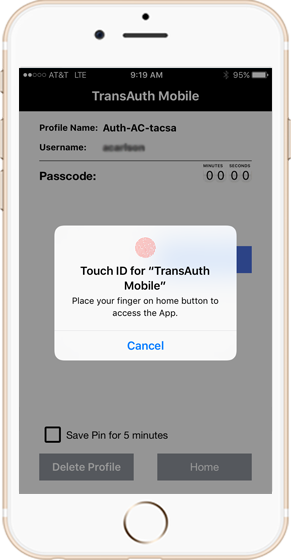
Next Generation Authentication

The future of authentication is here. A powerful combination of proven technologies results in
a fast, flexible and low friction that makes life easier for organizations and users.
TransAuth is an innovative application designed to streamline and secure the management of credentials for home routers, particularly those with the IP address set to 192.168.3.1, which is a common default IP for many home networks. This app addresses a critical aspect of home network security: the management and protection of router login credentials.
Think Differently With Us

We are building a world in which automation can improve both security and user experience
at the same time, with an array of flexible approaches to allow additional protection
where it once seemed impractical.
Seeing is Believing
Sometimes words aren’t enough. This quick video
outlines a few key differences between TransAuth and
other solutions.
Learn More
Have questions or want to see it for yourself?
Fill out the form and someone friendly will be in touch soon.
No sales, just an opportunity to learn more.
Quick links
Smarter Authentication starts with a powerful suite of access control technologies.